Cliff Crosland and Steven Wu are ushering in a new era of cybersecurity with Scanner, a groundbreaking platform designed to make petabytes of security data searchable in mere seconds. This technological leap promises to transform security operations by unlocking the full potential of artificial intelligence, enabling faster and more effective threat detection and response. The company has secured a significant Series A funding round, led by Sequoia Capital, signaling strong market confidence in its innovative approach to one of the most persistent challenges in modern enterprise security.
The Log Data Deluge: A Persistent Cybersecurity Headache
For years, Chief Information Security Officers (CISOs) and security engineers across Silicon Valley have grappled with an overwhelming challenge: managing the ever-increasing volume of security data. A decade ago, the landscape of enterprise software presented similar issues, and remarkably, the core problem remains the same. As one security leader poignantly described it, "We drown in logs we can’t afford to keep, and go blind on the logs we can’t afford to search."
This sentiment highlights the critical dilemma faced by organizations today. The sophisticated security tools deployed by enterprises, from firewalls and intrusion detection systems to application programming interface (API) gateways and identity management platforms, generate vast quantities of log data. Every API call, every login attempt, every network connection is meticulously recorded. To effectively investigate cyber threats, detect anomalies, and ensure compliance, security teams require access to this comprehensive historical data, often stretching back a year or more.
However, the traditional approach to managing this data presents significant financial and operational hurdles. Storing all this information in Security Information and Event Management (SIEM) systems, such as Splunk, incurs prohibitively high costs. Industry reports indicate that SIEM solutions can consume as much as 15% of a CISO’s entire annual budget, a figure that is unsustainable for many organizations, particularly growing tech companies.
Faced with this economic reality, companies are forced to make difficult compromises. A common strategy involves retaining only the most recent 10 to 30 days of logs within their SIEM for immediate access. The remainder of this invaluable data is often archived in cheaper cloud storage solutions, like Amazon S3. While cost-effective for storage, this approach renders the data effectively frozen and inaccessible for real-time analysis. The consequence? When a major security incident occurs, a compliance audit is mandated, or a forensic investigation is launched, security teams discover that the critical evidence they need is out of reach – opaque, unsearchable, and ultimately useless for timely decision-making. This creates a dangerous blind spot, leaving organizations vulnerable to prolonged breaches and undetected malicious activities.
The Genesis of Scanner: A Purpose-Built Solution
The genesis of Scanner emerged from a direct encounter with this widespread problem. The narrative gained traction when a member of the security team at Temporal, a prominent portfolio company of Sequoia Capital, described Scanner as "crazy fast." This powerful endorsement prompted an immediate investigation by the Sequoia team, leading to direct outreach to Cliff Crosland, one of Scanner’s co-founders.
The core insight behind Scanner, developed by Crosland and his co-founder Steven Wu, is elegantly simple yet profoundly impactful. Instead of attempting to adapt existing technologies to the problem of log data search, they reimagined the solution from the ground up, specifically for object storage environments. Their approach centers on a purpose-built inverted index. This innovative data structure maps field values directly to specific file regions within object storage systems like S3.
This architectural difference fundamentally alters the search paradigm. Instead of sifting through billions of individual log entries, Scanner’s technology allows queries to be narrowed down to only the precise slices of data that are relevant to the search. This means that a petabyte of log data, previously a daunting and unmanageable archive, becomes interactive and readily explorable. Queries that previously took hours, or even days, to complete can now be executed in a matter of seconds.
Furthermore, Scanner has integrated a sophisticated streaming detection engine. This engine operates continuously, processing tens of terabytes of data daily by running hundreds of detection rules in parallel. Crucially, it achieves this without the need to re-scan the entire dataset for each individual rule, a process that is both time-consuming and computationally expensive in traditional systems.
The Founders: A Blend of Expertise and Obsession
The founders behind Scanner, Cliff Crosland and Steven Wu, represent the ideal profile sought by venture capital firms like Sequoia Capital. Both are alumni of Stanford University’s Computer Science program, bringing a strong theoretical foundation and a deep understanding of complex systems. Their practical experience was honed as engineering leads at Accompany, a company that was subsequently acquired by Cisco. There, they were instrumental in building core data infrastructure under demanding, real-world production conditions.
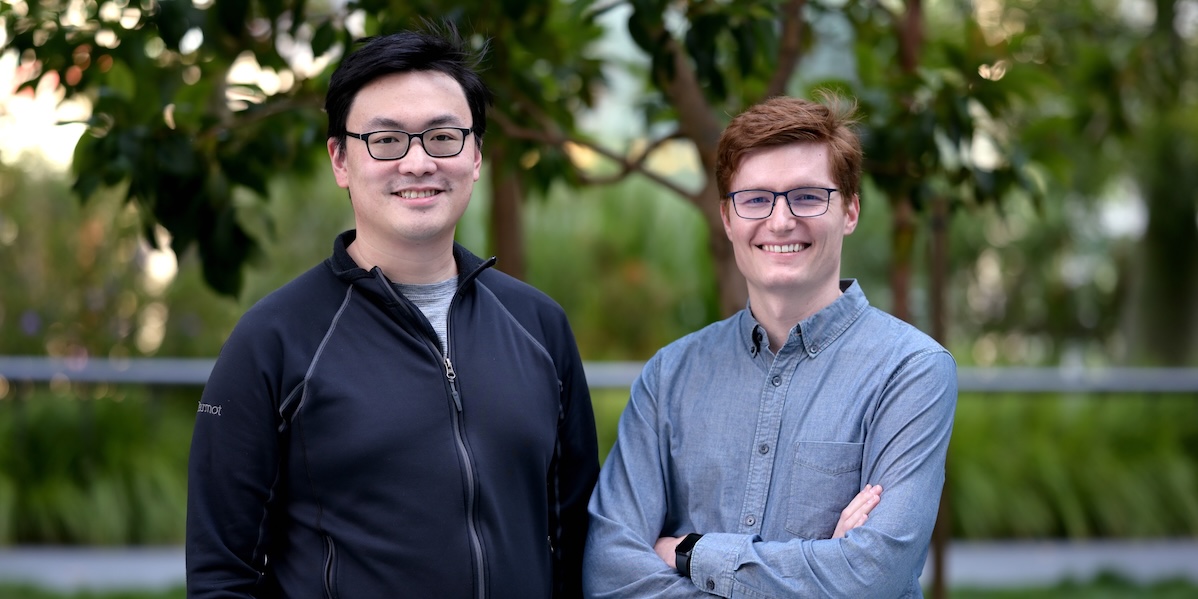
A defining characteristic of Crosland and Wu is their profound obsession with performance. This is not merely a preference; it borders on a philosophical commitment. They harbor a deep intolerance for systems that exhibit slow response times, believing that user experience and operational efficiency are inextricably linked to speed. This relentless pursuit of optimization, combined with their extensive technical expertise, has enabled them to engineer a solution that directly addresses the performance bottlenecks plaguing existing security data management platforms.
Early Adopters and Enthusiastic Endorsements
The traction Scanner has gained among its early customers is perhaps the most compelling testament to its efficacy. The platform is being utilized by a veritable "who’s who" of the cloud-native technology landscape, including industry leaders such as Notion, Ramp, Benchling, Confluent, Lemonade, and BeyondTrust. These companies, known for their technical sophistication and demanding operational environments, are not merely using Scanner; they are reportedly enthusiastic about its capabilities.
Benchling, for instance, made the strategic decision to replace a previous product following a substantial, unsolicited tenfold price increase from their incumbent vendor. The head of security engineering at Benchling lauded this move as "one of the best technical decisions their team had made," underscoring the significant value and improved performance Scanner delivered.
Ramp initially deployed Scanner to manage their security logs. However, the platform’s success and cost-effectiveness led them to expand its use to encompass application logs as well. This broadened adoption resulted in a direct reduction in their overall SIEM expenditure.
Perhaps one of the most forward-looking use cases comes from Notion. Their detection and response team has successfully developed an internal AI agent that leverages Scanner to autonomously conduct security investigations. This application directly points towards the future of cybersecurity operations, where intelligent agents will take on a significant portion of the analytical and investigative workload currently performed by human analysts.
The Dawn of AI-Driven Security Operations
The development at Notion is indicative of a broader paradigm shift. The cybersecurity industry is undeniably entering a new era, one where AI agents are poised to automate and accelerate the complex investigative processes that currently consume vast amounts of human time and resources. However, for these AI agents to function effectively, they require an environment that supports rapid iteration, constant questioning, and the ability to follow intricate threads of investigation. In such a scenario, query response times measured in minutes, let alone hours, become an insurmountable impediment.
Scanner’s exceptional speed is precisely what enables these advanced, agentic security workflows across a diverse range of organizations. The company’s recent release of its Managed Cloud Platform (MCP) has seen rapid adoption, with nearly a third of Scanner’s customers integrating it into their production environments within weeks of its launch. Moreover, AI-driven queries now account for an impressive 80% of all queries executed on the platform. This data point is not indicative of a nascent prototype or a promising beta program; it strongly suggests that the future of security operations is not only on the horizon but is actively arriving ahead of schedule, powered by Scanner’s capabilities.
Sequoia Capital Leads Series A Investment
Recognizing the transformative potential of Scanner and the strength of its founding team, Sequoia Capital has proudly announced its leadership of the company’s Series A funding round. This investment signifies a strong conviction in Scanner’s ability to redefine the cybersecurity infrastructure market, a sector long overdue for innovation.
"Cliff and Steven are exactly the kind of founders we look for," stated a representative from Sequoia Capital. "They possess a rare combination of deep technical expertise, a relentless focus on performance, and a clear vision for solving critical industry problems. Scanner’s ability to make petabytes of data searchable in seconds is not just an incremental improvement; it’s a fundamental shift that will empower organizations to leverage AI for more proactive and effective security."
Sequoia Capital’s partnership with Crosland, Wu, and the Scanner team is aimed at accelerating the company’s growth and solidifying its position as a leader in the next generation of security operations. The company is already making significant inroads, winning over the most technically forward-thinking organizations. Together, Scanner and Sequoia are poised to define the future of security infrastructure for the coming decade. The implications of this technological advancement extend beyond mere efficiency; they promise a more resilient and intelligent cybersecurity posture for businesses navigating an increasingly complex threat landscape.




