The global cybersecurity landscape has reached a critical inflection point where the traditional perimeter-based defense is no longer sufficient to safeguard sensitive organizational data. As 2025 approaches, the integration of artificial intelligence into the arsenal of cybercriminals has transformed security from a technical hurdle into a foundational pillar of business continuity. According to a landmark study published by Security Magazine, an overwhelming 93% of security leaders anticipate that their organizations will face daily AI-powered attacks by 2025. This shift represents a fundamental change in the "threat velocity," as automated systems can now identify and exploit vulnerabilities at speeds that far outpace human intervention.
The emergence of generative AI has specifically lowered the barrier to entry for sophisticated social engineering. Threat actors are increasingly deploying deepfake audio and video to impersonate high-level executives, while AI-generated phishing emails have become nearly indistinguishable from legitimate corporate communications. In this environment, the goal of a modern security department has shifted from the impossible task of total prevention to the pragmatic necessity of incident management. Incident management serves as a structured, repeatable framework designed to identify, analyze, and mitigate security breaches before they escalate into catastrophic failures.

The Regulatory Imperative: Compliance in an Era of Transparency
Beyond the immediate operational risks, the drive toward robust incident management is fueled by an increasingly stringent global regulatory environment. Legislative bodies worldwide have recognized that data breaches are not merely private corporate matters but public safety concerns. Consequently, frameworks such as the General Data Protection Regulation (GDPR) in the European Union and the Health Insurance Portability and Accountability Act (HIPAA) in the United States have set high benchmarks for how incidents are handled.
In recent months, the regulatory landscape has tightened further. The U.S. Securities and Exchange Commission (SEC) now mandates that public companies disclose "material" cybersecurity incidents within four business days of determining an incident is material. This shift toward rapid transparency means that organizations without a formalized incident management process risk not only financial penalties but also severe legal repercussions and a permanent loss of shareholder trust. For organizations operating in the financial sector, the Digital Operational Resilience Act (DORA) in the EU further emphasizes the need for comprehensive incident reporting and testing, making incident management a non-negotiable component of modern governance.
The Incident Management Lifecycle: A Chronology of Defense
Effective incident management is not a single action but a continuous lifecycle. To understand how organizations survive a modern breach, it is essential to examine the chronology of a typical response.
- Preparation: This phase involves the creation of incident response plans, the training of staff, and the deployment of monitoring tools. It is the foundation upon which all other steps are built.
- Detection and Analysis: This is the "Triage" phase. Security systems identify an anomaly—perhaps an unauthorized login from an unusual geographic location or a sudden spike in data egress. The incident management team must quickly determine the scope and severity of the threat.
- Containment: Once a threat is confirmed, the priority shifts to "stopping the bleed." This might involve isolating a compromised server from the rest of the network or disabling compromised user accounts to prevent lateral movement.
- Eradication and Recovery: After the threat is contained, the team works to remove the root cause, such as deleting malware or closing a backdoor. Recovery involves restoring systems from clean backups and returning to normal operations.
- Post-Incident Activity: Often called a "Post-Mortem," this final stage involves analyzing the breach to improve future defenses. It is a critical step for meeting compliance requirements and ensuring that the same vulnerability is not exploited twice.
Supporting Data: The Cost of Inaction
The financial implications of inadequate incident management are staggering. According to IBM’s "Cost of a Data Breach Report 2024," the average global cost of a data breach has risen to $4.88 million, a 10% increase over the previous year. However, the report also highlighted a significant "silver lining": organizations that utilized high levels of security AI and automation in their incident management processes saved an average of $2.22 million compared to those that did not. This data reinforces the argument that incident management tools are no longer a luxury but a necessary investment for fiscal responsibility.
Leading Incident Management Solutions for 2025
To navigate this high-stakes environment, organizations are turning to sophisticated platforms that integrate Security Information and Event Management (SIEM) with Security Orchestration, Automation, and Response (SOAR). Below are the seven leading tools currently defining the market.
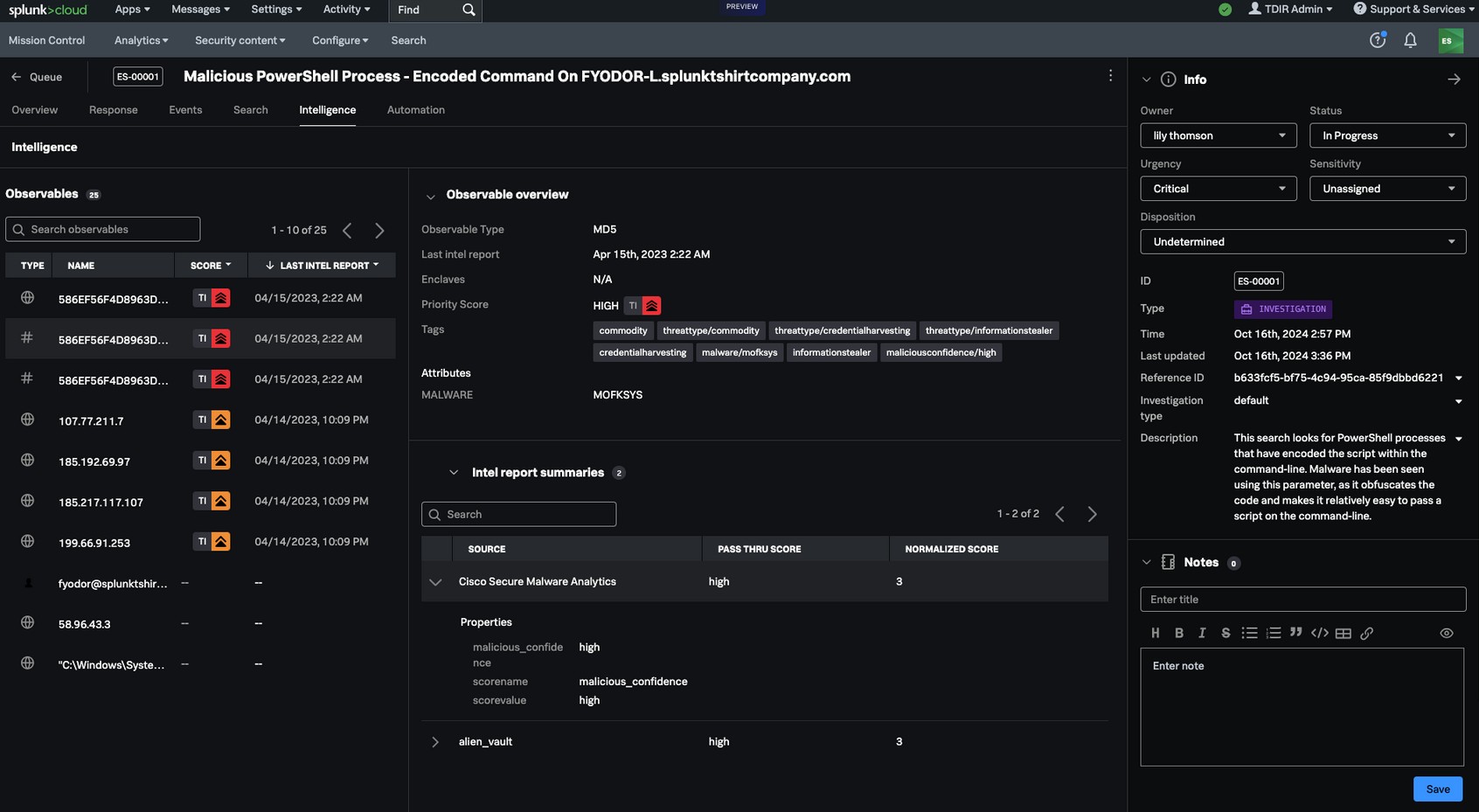
1. Splunk Enterprise Security (ES)
Splunk has long been the gold standard for security analytics. Following its high-profile acquisition by Cisco, Splunk Enterprise Security has doubled down on its "observability" mission. It allows organizations to ingest massive volumes of data from across their infrastructure and use advanced analytics to spot patterns that indicate a breach.
- Key Advantage: Its scalability makes it the preferred choice for global enterprises with complex, multi-cloud environments.
- Market Position: Splunk is increasingly viewed as an "intelligence hub" that provides a unified view of both IT operations and security.
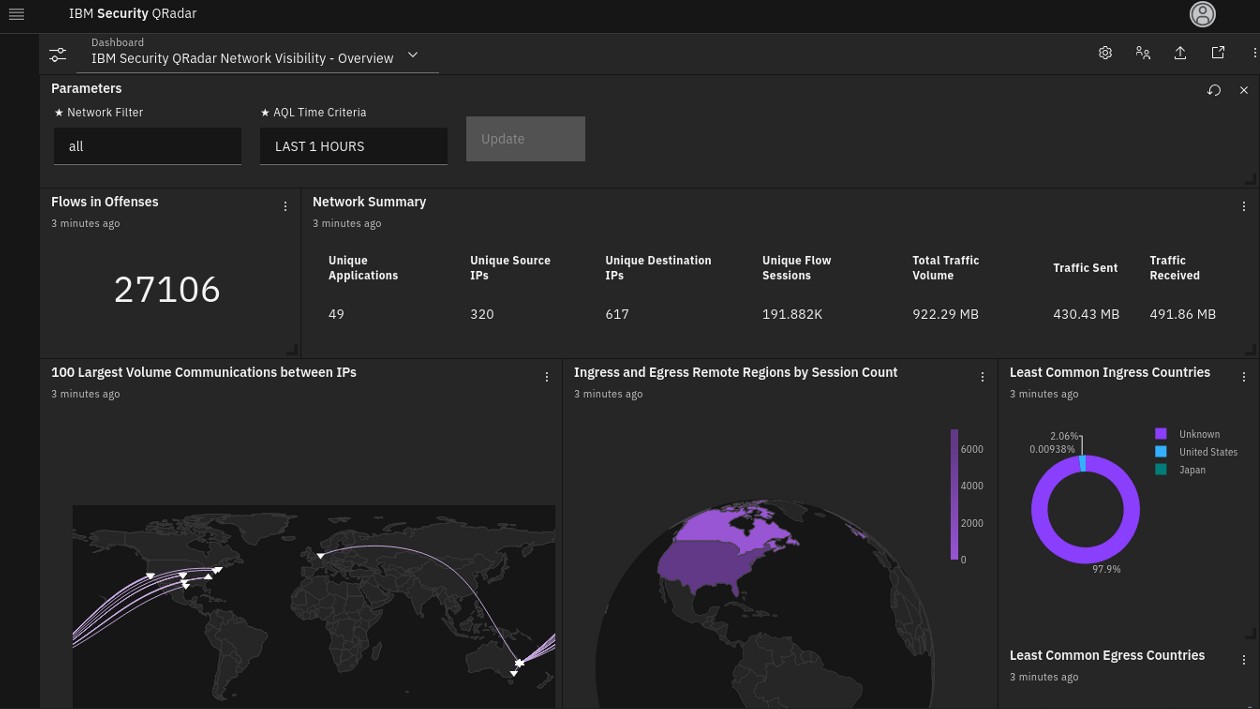
2. IBM QRadar
IBM QRadar distinguishes itself through its "Advisor with Watson" integration, which brings cognitive computing to the security operations center (SOC). It automates the labor-intensive process of investigating thousands of daily alerts, allowing human analysts to focus on high-priority threats.
- Strategic Shift: IBM recently announced a strategic partnership to transition its QRadar SaaS assets to Palo Alto Networks, a move that signals a consolidation of the market toward integrated platforms.
- Key Advantage: Exceptional threat intelligence gathered from IBM’s global research network.
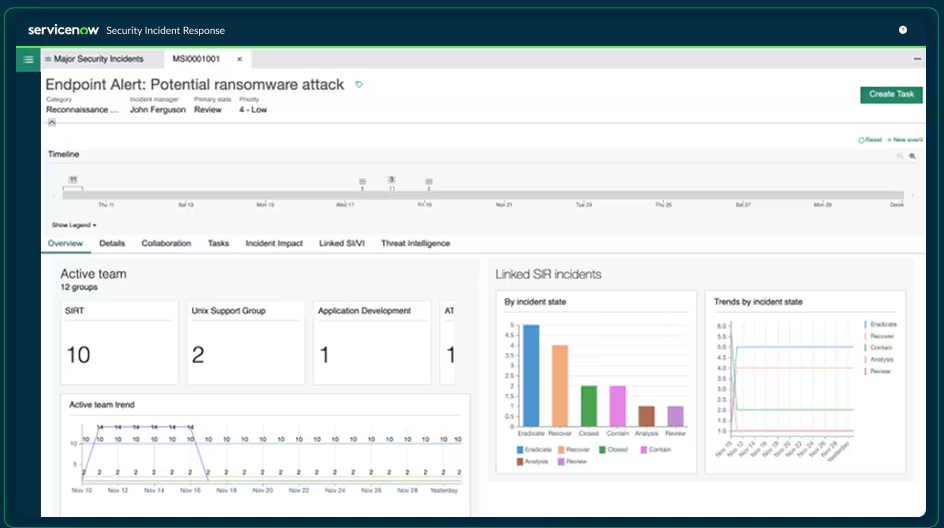
3. ServiceNow Security Incident Response (SIR)
ServiceNow approaches incident management from a workflow perspective. Rather than just being a technical tool, SIR bridges the gap between the IT department and the security team. It uses the "ServiceNow Dashboard" to track the progress of a response, ensuring that every step of the compliance checklist is completed.
- Key Advantage: It is ideal for organizations that already utilize the ServiceNow ecosystem for IT Service Management (ITSM), providing a seamless transition from "ticket" to "security incident."
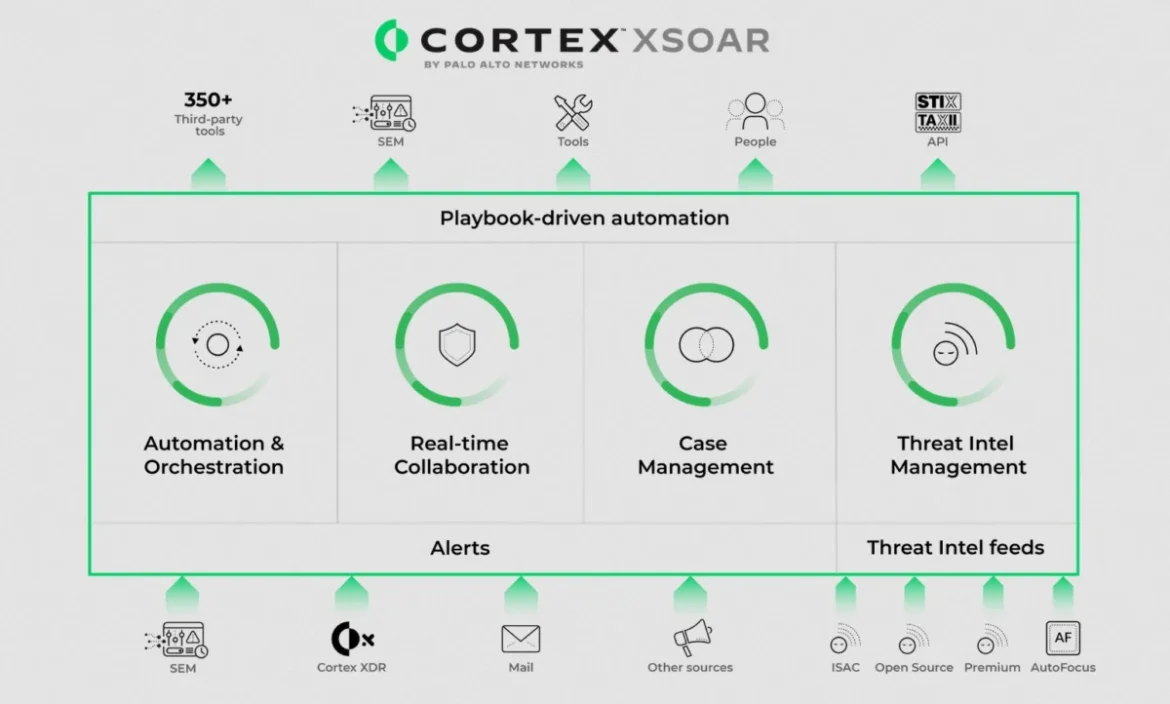
4. Palo Alto Networks Cortex XSOAR
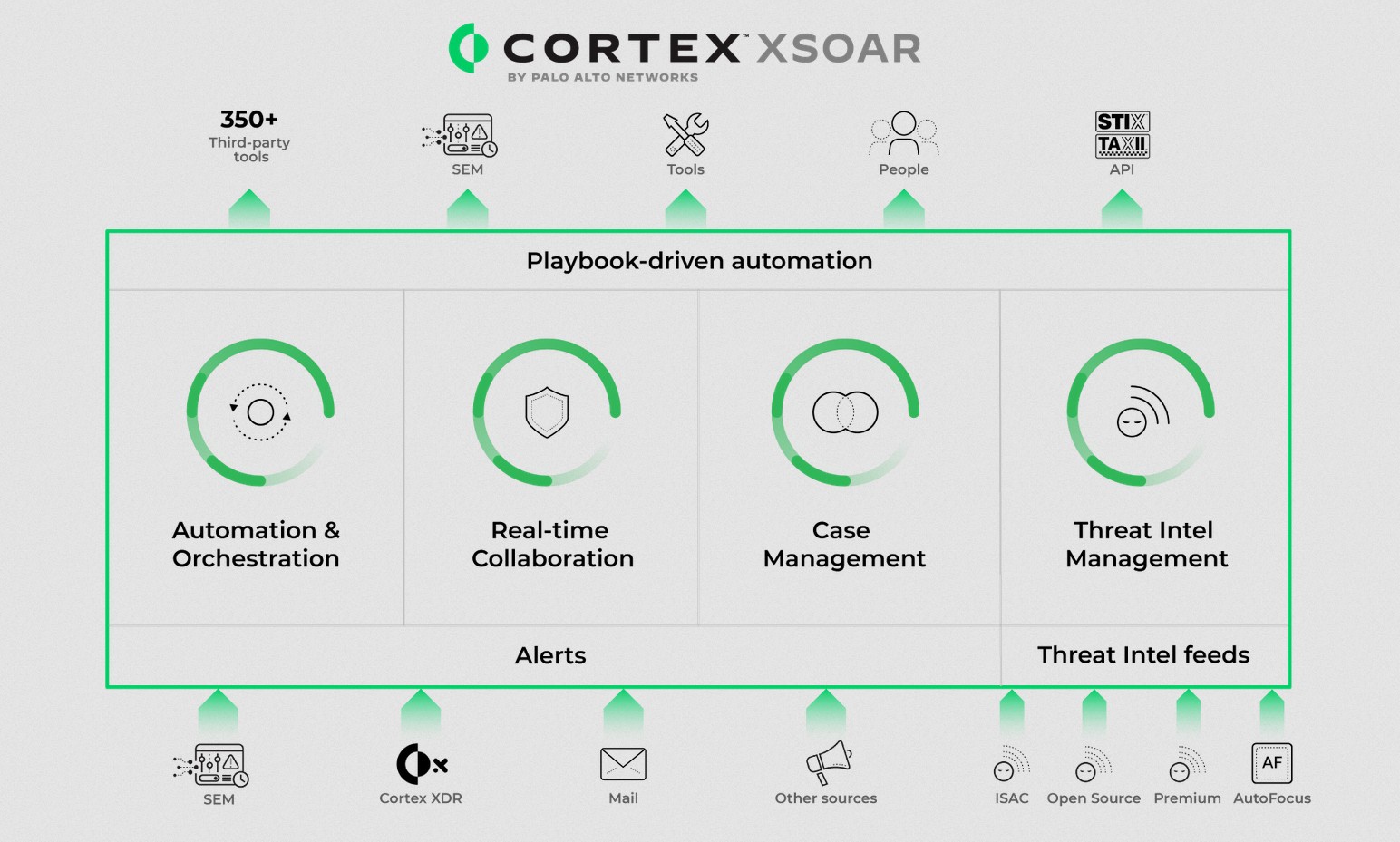
Cortex XSOAR is widely considered the pioneer of the SOAR category. It features a "War Room" functionality where security analysts can collaborate in real-time. By using "playbooks," Cortex XSOAR can automate hundreds of standard response actions, such as blocking an IP address or resetting a password, without human intervention.
- Key Advantage: The platform’s extensive integration library allows it to work with virtually any other security tool in a company’s stack.
5. Rapid7 InsightIDR
Rapid7’s InsightIDR is designed for the modern, hybrid workforce. It focuses heavily on User and Entity Behavior Analytics (UEBA). In an era of AI-driven credential theft, InsightIDR excels at identifying when a legitimate user’s account is behaving in a suspicious manner, such as accessing sensitive files they have never touched before.
- Key Advantage: It offers a shorter "time-to-value" compared to more complex SIEMs, making it a favorite for mid-sized enterprises.
6. Microsoft Sentinel
As a cloud-native SIEM/SOAR platform, Microsoft Sentinel has seen explosive growth. It leverages the power of the Azure cloud to provide nearly infinite scale. With the introduction of "Microsoft Copilot for Security," Sentinel now allows analysts to use natural language queries to investigate threats, significantly reducing the technical expertise required to manage an incident.
- Key Advantage: For organizations already heavily invested in the Microsoft 365 ecosystem, Sentinel offers unparalleled visibility into email and identity threats.
7. ManageEngine Log360
ManageEngine Log360 provides a comprehensive yet accessible solution for organizations that need to meet compliance standards like GDPR and PCI DSS without the astronomical costs of enterprise-grade SIEMs. It offers robust log management, auditing, and real-time alerting.
- Key Advantage: It is highly regarded for its ease of use and its ability to provide clear, audit-ready reports for regulatory bodies.
Broader Impact and Future Implications
The rise of AI-driven threats has created an "arms race" between attackers and defenders. As cybercriminals use AI to automate the creation of malware, security teams must use AI to automate the response. This evolution is fundamentally changing the role of the cybersecurity professional. The "analyst of the future" will spend less time manually digging through logs and more time managing the AI agents that perform the initial triage.
Furthermore, the focus on incident management is fostering a culture of "cyber resilience" rather than just "cybersecurity." Resilience acknowledges that breaches are inevitable and focuses on how quickly an organization can bounce back. This cultural shift is expected to influence insurance premiums, as cyber-insurers begin to reward companies that can demonstrate robust, automated incident response capabilities with lower deductibles and better coverage.
In conclusion, the data is clear: the threat of AI-driven attacks is no longer a futuristic scenario but a present-day reality. Organizations that fail to implement a structured incident management strategy—supported by the advanced tools outlined above—are leaving themselves vulnerable to catastrophic financial and reputational damage. As we move into 2025, the ability to manage an incident will be the ultimate differentiator between companies that thrive in the digital age and those that fall victim to its inherent risks.